-
Notifications
You must be signed in to change notification settings - Fork 18k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
crypto/ed25519: add edge case tests #40478
Comments
|
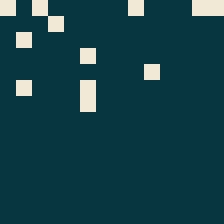
https://github.com/hdevalence/ed25519consensus is a fork of crypto/ed25519 with a Relevant to this issue, the The difference between (my interpretation of) RFC 8032 and the current Go behaviour can be visualized as follows:
On the left, the dark shade indicates MUST-reject (according to RFC 8032, which was written after this implementation and is incompatible with it), medium indicates MAY-accept, light indicates MUST-accept. (RFC 8032 does not require implementations to agree on whether signatures are valid). On the right, dark and light indicate rejected and accepted, respectively. Note that all of these test cases require carefully crafted public keys. Therefore, there's no security issue with the signatures themselves, because an attacker who can control the public key can sign any message whatsoever. The problem is just the inconsistency, which could allow, e.g., a malicious party to inject faults into a consensus algorithm and cause consensus divergence. |
|
There's more context in @hdevalence's article here: https://hdevalence.ca/blog/2020-10-04-its-25519am Indeed, since there is no security risk we probably should not change the behavior now and risk forking some blockchains. We'll add test cases and a paragraph to the docs. |
|
Thanks for the report @FiloSottile and for the details and work @hdevalence! We didn't get much action for the edge cases and Go1.16 is due, thus I shall kindly punt this to Go1.17. @hdevalence, it would be awesome to have you as a contributor to the Go project, your work on ed25519 is much appreciated too. I kindly nudge you @hdevalence to feel free to send some changes for Go1.17 and we'll review. |
|
Change https://golang.org/cl/304349 mentions this issue: |

We'll want to add tests for the edge cases that led to #40475.
Ideally, they would go into Wycheproof and run from there, making sure they run against all architectures.
/cc @hdevalence @katiehockman
The text was updated successfully, but these errors were encountered: